DCI Memorandum on NIST Standards Transitions and "Non-FIPS Mode"
Approved 1 July 2020
Digital Cinema Initiatives, LLC, Member Representatives Committee
[Click for a PDF of this Memorandum]
On December 19, 2019, DCI issued a memorandum informing the d-cinema industry of NIST's announcements regarding the transition to the FIPS 140-3 standard1. The key dates of this transition are (1) the start of Media Block (MB) submissions for FIPS 140-3 testing by CMVP labs on September 22, 2020, and (2) the end of MB submissions for FIPS 140-2 testing by CMVP labs on September 22, 2021.
In addition to this transition, there are two other NIST standard changes impacting MB designs:
- SSP800-90B is effective November 8, 2020, for all new submissions (or any security relevant revalidation submissions) for FIPS 140-2 or FIPS 140-3 cryptographic module validation by a Cryptographic Module Validation Program (CMVP) test lab.2
- SSP800-56Br2 is effective January 1, 2021. FIPS 140-2 and 140-3 validated modules that are not compliant to any applicable requirement will be moved onto the historical listing by CMVP.3
While DCI's customary practice is to maintain compliance to all NIST/FIPS requirements, it is our position that (1) the security impacts of the above standards changes are minimal, and (2) equipment manufacturers should focus on the FIPS 140-2 to FIPS 140-3 transition and not be additionally impacted by the SP800-90B and SP800-56Br2 effective dates.
DCI therefore elects to allow MB designs to defer SP800-90B and SP800-56Br2 standards changes for FIPS 140-2 validated modules. Compliance is required for FIPS 140-3 designs.
DCI MEMORANDUM ON FIPS 140-3
Approved 19 December 2019
Digital Cinema Initiatives, LLC, Member Representatives Committee
[Click for a PDF of this Memorandum]
The long anticipated arrival of FIPS 140-3, "Security Requirements for Cryptographic Modules" was announced in the Federal Register on May 1, 2019. FIPS 140-3 will supersede FIPS 140-2, which is currently used by the digital cinema community.1
Pursuant to the current NIST schedule (detailed below), devices will be able to be submitted for CMVP testing to FIPS 140-3 starting September 22, 2020. One year later, on September 22, 2021 no new devices may be submitted to a CMVP lab for testing to FIPS 140-2, effectively sunsetting FIPS 140-2.
DCI Compliance to FIPS 140-3
DCI believes the new standard maintains assurance of a satisfactory threshold of security for the d-cinema industry. DCI will require FIPS 140-3 compliance in new devices once FIPS 140-2 sunsets in September 2021. Therefore, DCI strongly urges suppliers to create new designs to FIPS 140-3.
DCI will embrace the migration to FIPS 140-3 by publishing new errata that evolve the Digital Cinema System Specification (DCSS) to include references to both FIPS 140-2 and 140-3 for purposes of Media Block FIPS certification. In the year of overlap between the start of 140-3 testing and termination of 140-2 testing, Media Block suppliers will be free to choose under which standard they seek certification.
DCI will continue its policy that once a Media Block (or any Secure Processing Block) has been FIPS certified, the design will continue to be recognized as DCSS compliant. For purposes of future-proofing Media Blocks, DCI strongly urges suppliers to design to FIPS 140-3 sooner than later.
FIPS 140-3 Details and References
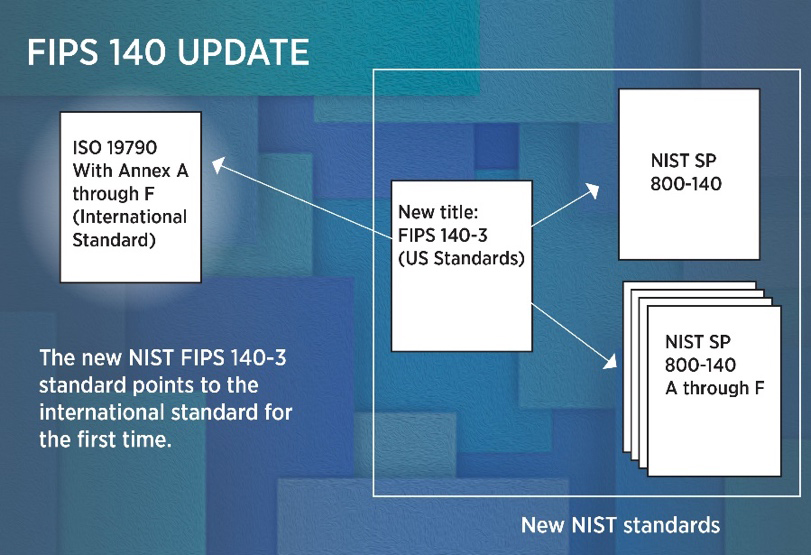
FIPS 140-3 relies upon two existing international standards: 2
- International Organization for Standardization/International Electrotechnical Commission (ISO/IEC) 19790:2012(E) Information technology – Security techniques – Security requirements for cryptographic modules; and
- ISO/IEC 24759:2017(E) Information technology – Security techniques – Test requirements for cryptographic modules.
The new NIST Special Publication (SP) series 800-140x will specify updates, replacements, or additions to the currently-cited ISO/IEC standards, as necessary. The SP 800-140x documents will consolidate implementation and administrative guidance.3
FIPS 140-3 testing via the Cryptographic Module Validation Program (CMVP)4 schedule details are:5
Implementation Schedule
Current Schedule- 9-26-2019
| Date |
Activity |
March 22,2019
|
FIPS140-3 Approved
|
|
September 22,2019
| FIPS140-3 Effective Date
Drafts of SP 800-140x available for public comment (See status page) |
|
March 22, 2020
|
Publication ofSP 800-140x documents
Implementation Guidance updates
Tester competency exam updated to include FIPS140-3
Updated CMVP Program Management Manual
|
| September 22, 2020
|
CMVP accepts FIPS 140-3 submissions
|
|
September 22, 2021
|
CMVP stops accepting FIPS 140-2 submissions for new validation certificates
|
|
September 22,2026
|
Remaining FIPS140-2 certificates moved to Historical List |
Regarding reliance on the ISO/IEC standards, NIST states "the newly released FIPS 140-3 modernizes the standard and essentially makes the U.S. standard a 'pointer' indicating that manufacturers should now use the international standard, which NIST helped to develop. Any product that adheres to the international standard - known as ISO 19790 - will therefore use an encryption approach that is acceptable both within and outside the United States."